Cybersecurity Bootcamp
Join our Cybersecurity Bootcamp to learn a remote-friendly job that pays ~$80,000 to start. Choose between a 3.5-month, full-time program or a 7-month, part-time program for more flexibility.
Award-winning online job training and support designed for your real life
background needed
2.5k+ reviews
*Get a relevant job in 10 months or your tuition back when you complete our included Career Services package and make a good-faith effort to find a job. Details in our Terms of Use.
What do Cybersecurity professionals do?
Cybersecurity professionals protect the world’s digital infrastructure: defending systems, networks, and data against increasingly sophisticated threats. At TripleTen, you’ll master the essentials and go further with an immersive AI security sprint that prepares you for the newest frontier in the field: safeguarding AI-powered systems.
Where can your Cybersecurity career path take you?
Cybersecurity is a high-income career track with high potential for growth
You after TripleTen


How you get a new career in 7 months:
Exclusively at TripleTen: the most current & comprehensive prep for AI cybersecurity threats.
There’s a global cybersecurity workforce shortage:
There’s a global cybersecurity workforce shortage:
Our grads get great jobs with both startups and industry giants
2 weeks
insights
TripleTen’s Cybersecurity bootcamp is flexible, with no set meeting times for participants. It’s not self-paced—there are project deadlines and an expected graduation date—but we offer extensions and opportunities for breaks.
Download.pdfFundamentals
This module lays that groundwork. You'll get comfortable reading IP addresses, mapping out network topologies, and using monitoring tools to watch traffic in real time—spotting anything that looks out of place. From there, you'll dig into scanning and enumeration, learning how attackers find exposed assets and what you can do to make your systems harder to profile. The module wraps up with a practical look at cybersecurity frameworks: you'll size up an organization's risk, write security policies, and use the NIST CSF to build a plan that actually addresses the threats. Walk away knowing how to evaluate network design, catch anomalies early, and put together a clear, structured response when something goes wrong.
Hard Skills
- NIST CSF
- Nmap
- Network topology
- Traffic monitoring
- Risk assessment
- CMDB
Soft Skills
- Analytical thinking
- Adaptability
- Time management
- Problem-solving
- Documentation
- Attention to detail
Incident Response
This module is about making sure you're ready to act when a security incident hits. You'll start by getting to know the most common threats and attack vectors, then figure out which mitigations will shrink an organization's exposure the most. From there, you'll build formal incident response playbooks for real scenarios: phishing attempts, malware outbreaks, data breaches, and DDoS attacks. Using NIST standards as your benchmark, you'll review and sharpen existing response plans so that when something goes sideways, the team knows exactly how to contain the damage, keep stakeholders informed, and make sure the same thing doesn't happen twice.
Hard Skills
- Attack surface analysis
- Malware analysis
- Threat modeling
- DDoS mitigation
- Incident response plan development
- Playbook creation (phishing, malware, DDoS, data breach)
Soft Skills
- Critical thinking
- Technical writing
- Decision-making
- Prioritization
Vulnerability Management
This module walks you through the entire vulnerability management process, from locking down networks and standing up a security operations center, to using virtualization to breathe new life into outdated infrastructure. You'll run formal vulnerability assessments, make sense of scan results, and rank risks by how serious they actually are. Authorized penetration testing helps you confirm the most critical findings aren't just theoretical. The module also puts a real emphasis on communication: you'll present your findings in industry-standard formats and make the case to non-technical leaders—clearly and convincingly enough to get the green light for security improvements.
Hard Skills
- Network hardening and virtualization
- SNOC
- Threat modeling
- Vulnerability scanning
- Penetration testing
- Vulnerability severity scoring (e.g., CVSS)
Soft Skills
- Evidence-based reasoning
- Data presentation
- Project planning
Investigating Incidents
The final module is where everything comes together. You'll build out a real monitoring environment—deploying a SIEM, pulling in logs from key endpoints, and stress-testing the whole setup with adversary emulation tools like Atomic Red Team to make sure nothing slips through. Then comes the investigative work: using Splunk to triage alerts and dig into suspicious activity—odd file changes, strange network traffic, questionable logins, and signs of data being quietly siphoned out. You'll sharpen your ability to tell a genuine incident from a false alarm, and you'll document everything the way employers actually expect. By the end, you're not just technically capable—you're job-ready.
Hard Skills
- SIEM deployment
- Log aggregation
- Adversary emulation (Atomic Red Team)
- Splunk
- False-positive analysis
- Alert triage
- Traffic analysis
Soft Skills
- Evidence-based reasoning
- Data presentation
- Project planning
Fundamentals
In this module, students get hands-on with the core building blocks of cybersecurity—running scans and enumeration exercises to identify and catalog a company's assets into a CMDB. They learn to read results from standard scanning tools and put defensive measures in place to keep device identities hidden from would-be attackers. From there, the module shifts into cybersecurity frameworks, where students assess an organization's risk profile, keep tabs on assets continuously, and work through how to respond when incidents hit. Working within the NIST Cybersecurity Framework (NIST CSF), they size up a mid-sized business's security posture and put together a mitigation plan—complete with stronger policies and procedures—to keep the business running and head off future incidents.
Hard Skills
- Network scanning
- CMDB
- NIST CSF
- Security policy
- Incident response
Soft Skills
- Analytical thinking
- Attention to detail
- Problem-solving
- Organizational skills
Incident Response
This module is all about understanding and tackling the cybersecurity threats that organizations run into most often. Students learn to threat model an organization, pin down attack vectors, and figure out which mitigations to prioritize in order to shrink the attack surface. They build out structured playbooks for common incident scenarios—phishing, malware, data breaches, DDoS attacks—and then dig into a project that asks them to critically tear apart a poorly executed incident response plan from a ransomware attack and rebuild it to hold up against NIST standards. By the end, students walk away with the practical know-how to protect organizations from repeating the same mistakes and to lead a coordinated, effective response when things go sideways.
Hard Skills
- Threat modeling
- Attack vector identification
- Attack surface reduction
- Incident response playbook development
- NIST
- Mitigation strategy planning
Soft Skills
- Critical thinking
- Decision-making
- Prioritization
Vulnerability Management
This module takes students through the full lifecycle of vulnerability management from start to finish. They kick things off by hardening networks, standing up a Security Network Operations Center (SNOC), getting virtualization in place, and tightening up authentication practices. From there, they run formal vulnerability assessments—inventorying assets, executing scans, making sense of the results, and ranking remediations by severity. Students then move into penetration testing to validate and confirm the most critical findings, follow through with remediation, and package everything into industry-standard report formats. CompTIA Security+ fundamentals are woven throughout, with students starting exam prep through focused study methods including Anki flashcard decks.
Hard Skills
- Network hardening
- SNOC
- Virtualization
- Vulnerability severity analysis
- Penetration testing
Soft Skills
- Executive-level communication
- Analytical reasoning
- Time management
Investigating Incidents
This module trains students to dig into real-world security incidents across physical, virtual, and cloud environments. Students get comfortable securely managing networks, spinning up continuous monitoring systems, and pulling in security-critical logs from endpoints. They work through alerts and anomalies, learning to tell genuine incidents apart from false positives, and put together the right response plans for each. The module then takes things up a notch—students track down complex attacks using SIEM tools and the MITRE ATT&CK framework to map out attacker TTPs, writing targeted queries to work through the evidence. Everything wraps up with students authoring a formal incident investigation report that lays out findings and recommendations for both technical teammates and non-technical stakeholders.
Hard Skills
- Secure network management
- MITRE ATT&CK framework
- Log aggregation
- Threat detection and analysis
- False-positive analysis
- Alert triage
- Traffic analysis
Soft Skills
- Adaptability
- Collaboration
- Project planning
CompTIA Security+
The final module gets students ready to sit for the CompTIA Security+ certification exam and pass it. Building on the groundwork laid earlier in the program, students tackle the more advanced exam domains, work through hands-on exercises, and take practice exams to spot and fill any gaps in their knowledge. Solid exam strategies and continued use of study tools help lock in retention across all the key topic areas. Earning the certification tells employers that a student knows their stuff—it's a recognized industry credential that gives job applications a real boost and builds professional credibility in the field.
Hard Skills
- Hands-on cybersecurity exercises
- Practice exam performance
- Knowledge retention techniques
Soft Skills
- Self-discipline
- Stress management
Free bonus course for new students
Free
Computer Literacy
“Not a tech person”? Don’t know a browser from an OS? Take this course to get up to speed! Learn how to use a computer and industry-standard apps so you’re ready to break into tech.
or pre-requisites.
with regular project
deadlines.
Build professional skills using industry-standard tools
The TripleTen online Cybersecurity bootcamp experience is designed for learning success—and achieving your goals

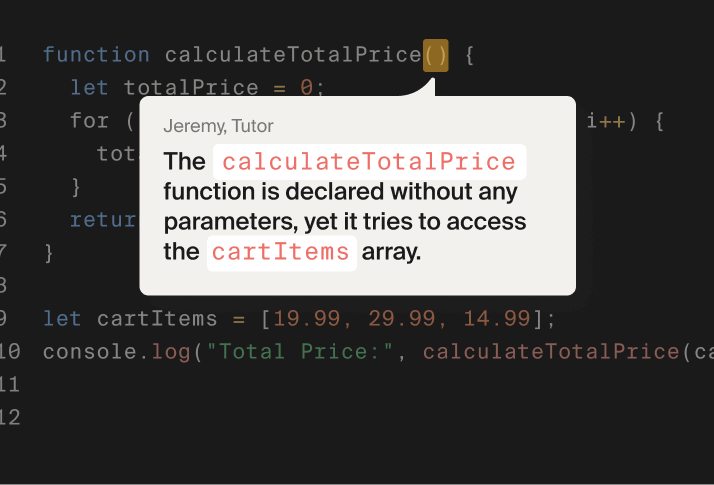
1-on-1 tutoring from industry professionals
Get your Cybersecurity skills from industry pros committed to making challenging concepts accessible—and helping you succeed

Get hired for a career-track role with our help
You’ll study more than network security at our Cybersecurity bootcamp—you’ll learn how to get job search security. One-on-one career coaching preps you with interview skills and resume and portfolio design, while AI automation helps power your search.

Of course! We will also cover your first CompTIA Security+ exam
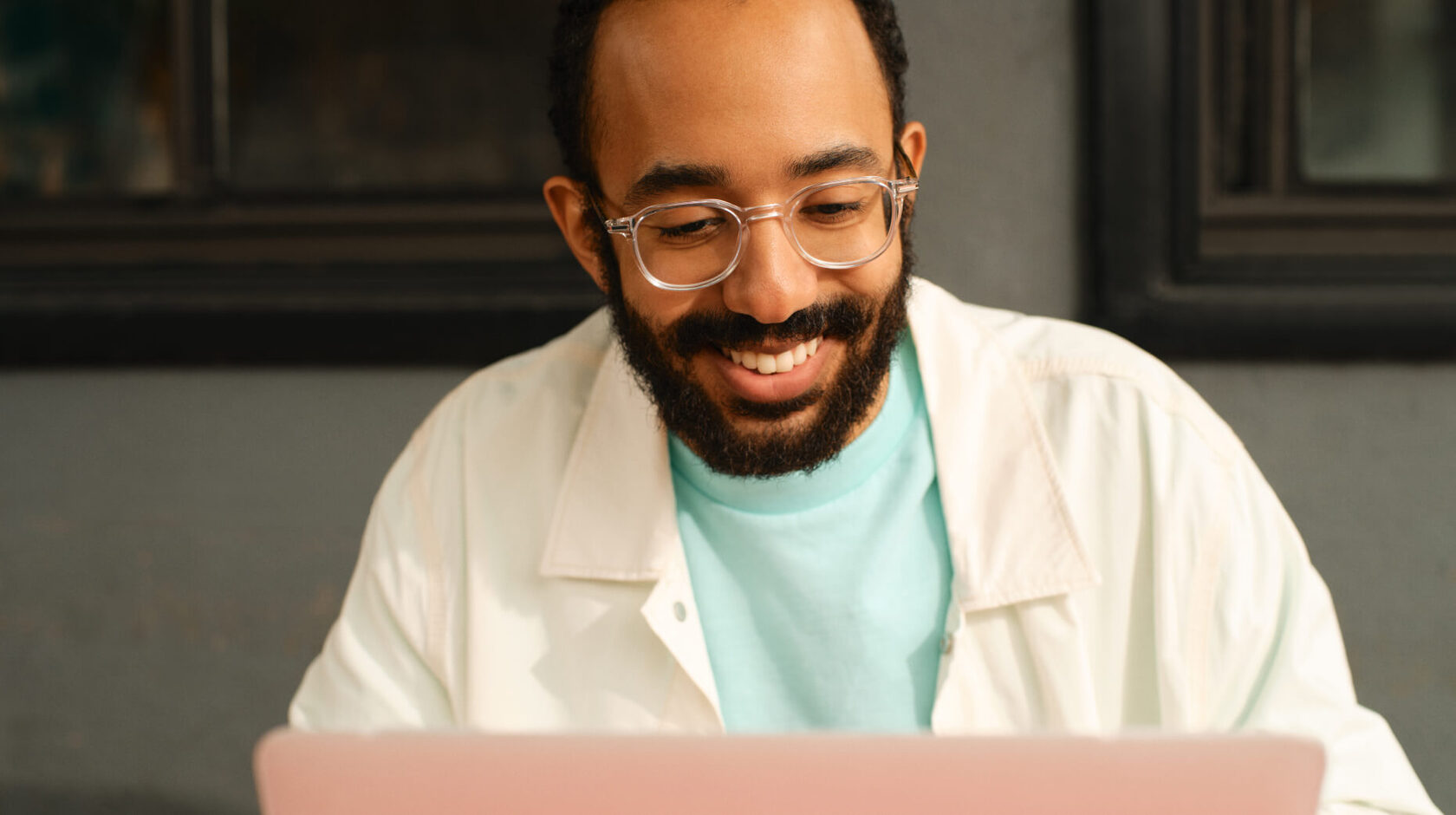
2,600+ TripleTen alumni. 80% of graduates had zero coding skills or previous tech-related experience

“I had a lot of great experiences with the tutors. Whenever I needed help, they were there.”
Full story
“I had a lot of great experiences with the tutors. Whenever I needed help, they were there.”
Full story4.8/5 across 2,500+ reviews on trusted platforms
Featured in
We believe that you’ll get into tech in 10 months. In fact, we put money on it.
the included career prep
and coaching programs.
and stay in touch with your career coach
The TripleTen money-back
guarantee is legally binding.
For details, please see our
Terms of use
We also have a fair refund policy
After starting our Cybersecurity Bootcamp, you have 2 weeks to withdraw with a 100% refund. After that, you can get a partial refund on a transparent schedule. Check our Terms of Use for more info.
Learn in a way that fits your life—anytime, anywhere—with constructive feedback and top-notch support.
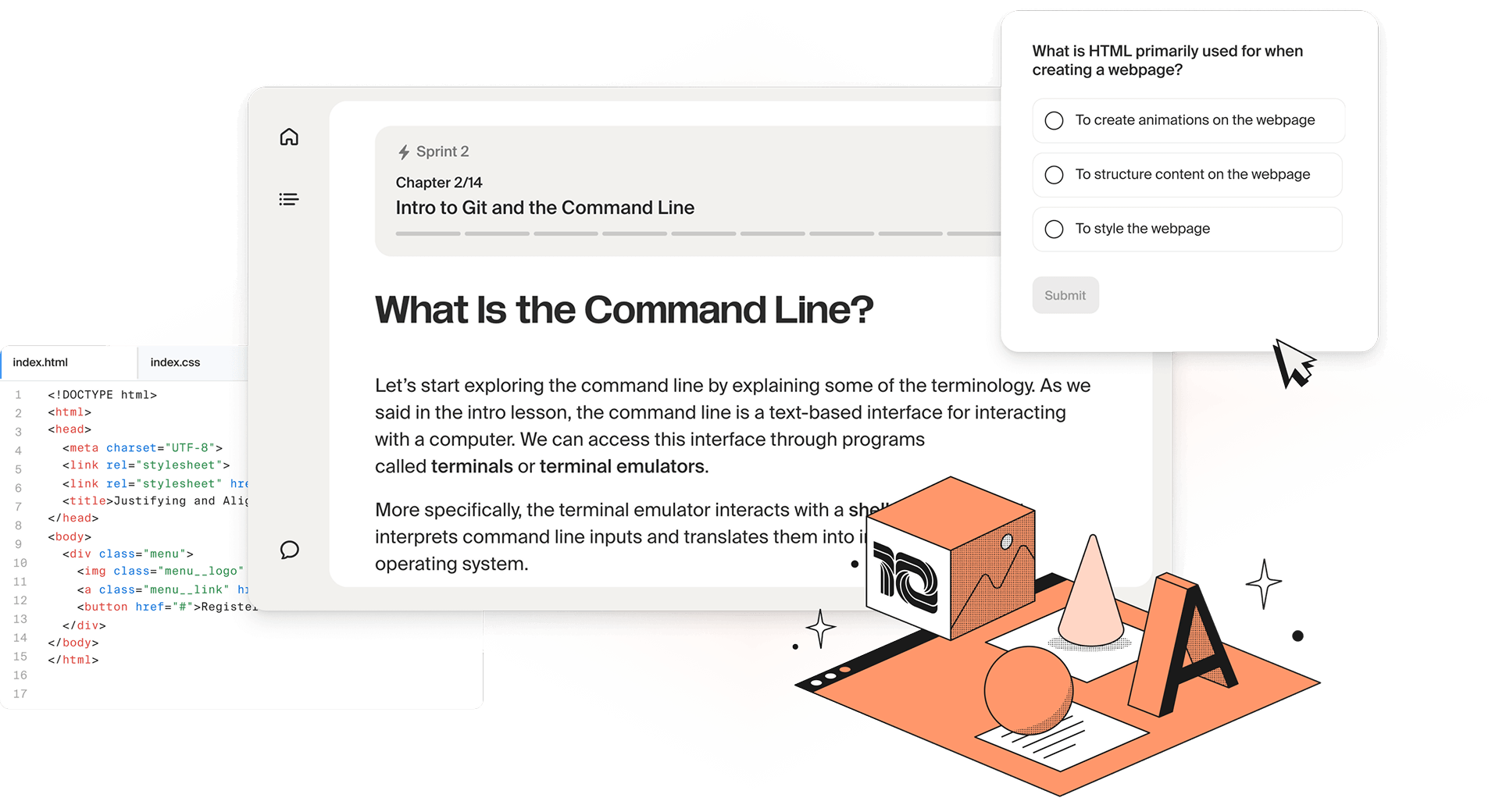
Practice and improve your coding skills with line-by-line code review and personal feedback from your tutors
Learn Cybersecurity the way you’d learn on the job—with detailed feedback and help from experienced Cybersecurity Analysts.
Reach out to your learning coach to talk through any issues you encounter. Sometimes, we all just need to talk to someone...

You’re never alone—our tutors always have your back
Become a magnet for recruiters with a personal career coach and AI job-hunting tools
Check our other
bootcamps
FAQ
Complete FAQWhat is a Cybersecurity bootcamp, and how is it different from a degree?
What is a Cybersecurity bootcamp, and how is it different from a degree?
TripleTen’s cybersecurity bootcamp is an intensive, skills-centered program that gets you job-ready in months, not years. A traditional degree takes four years and involves broad academic theory. A bootcamp focuses on skills employers need — vulnerability assessments, network security, penetration testing — so you spend less time in school and more time building a career.
How does the admissions process work?
How does the admissions process work?
There is no admissions process or prerequisites to join TripleTen programs. Just book a call with an advisor. It’s that simple. You’ll get your questions answered about the cybersecurity career path and whether this program is right for your goals. There are no barriers to joining TripleTen—all you need is motivation, determination, and a commitment of about 20 hours a week.
Are cybersecurity bootcamps worth it?
Are cybersecurity bootcamps worth it?
For most people who are making a career change, yes, a bootcamp is worth it if you intend to become a cybersecurity specialist and don’t want to spend years studying. Our online cybersecurity program provides practical knowledge and skills that make you valuable to employers.
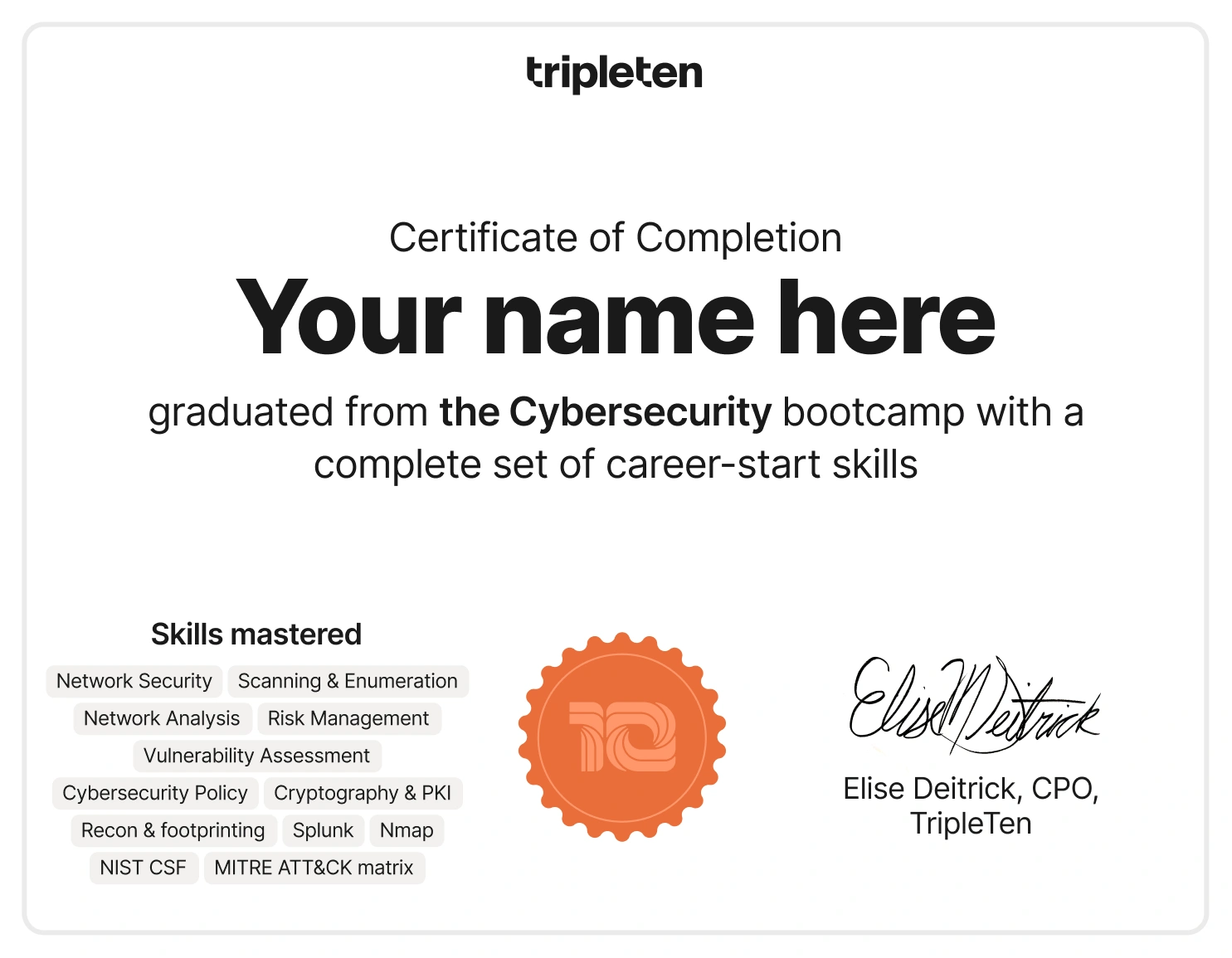
Will I get a certificate when I graduate?
Will I get a certificate when I graduate?
You’ll graduate from your cybersecurity bootcamp with a completion certificate from TripleTen, as well as the industry-recognized CompTIA Security+ certification.
What will I learn in the TripleTen cybersecurity program?
What will I learn in the TripleTen cybersecurity program?
The TripleTen Cybersecurity program gives you hands-on training on the latest security technologies and methodologies. You’ll learn about:
- Malware and virus threats
- Network security controls
- Cryptography
- Vulnerability testing methodologies
- Risk management
- Security procedures and disaster recovery
- AI vulnerabilities and tools
Additionally, you’ll acquire skills like critical thinking and communication to help you succeed in the workplace when explaining technical concepts to non-technical colleagues.
Can I keep working while I study?
Can I keep working while I study?
80% of our graduates had a full-time job while they studied: we intentionally make our programs flexible, with no mandatory meeting times. You study and practice on your schedule, and turn in projects on set deadlines. Our guidance team is online for most of the day and the tech support team is online 24/7. Together, they’re by your side to give you all the support you need to meet sprint deadlines.
How much does the program cost and what are the payment options?
How much does the program cost and what are the payment options?
Tuition cost depends on the payment option. The most affordable is the upfront payment, starting at $10,500. Flexible payment options are available too.
We offer three payment options:
1. Upfront before you start.
2. Monthly installments while you study.
3. Learn now, pay later options.
How long does it take to complete a cybersecurity bootcamp?
How long does it take to complete a cybersecurity bootcamp?
TripleTen’s program takes 7 months part-time (15-20 hours a week of study) or 3.5 months full-time (40 hours a week). Exact timelines depend on your pace, so check with an advisor for specifics.
What is TripleTen’s job placement rate?
What is TripleTen’s job placement rate?
In 2025, two-thirds of grads found jobs within 10 months of graduation. Outcomes can vary depending on factors like your background, location, and the effort you put into your job search — but our results are strong and competitive within the industry.
We can’t control hiring trends, but we pride ourselves on transparency. That’s why we publish our results and encourage you to review the data yourself in our Student Achievement Highlights, where you’ll find statistics on hiring timelines and employment outcomes.
What career paths and salary can I expect after completing the Cybersecurity bootcamp?
What career paths and salary can I expect after completing the Cybersecurity bootcamp?
Entry-level roles include SOC Analyst, Security Analyst, Junior Risk Analyst, Junior Security Engineer, and Information Security Analyst. From there, you can specialize — penetration testing, cloud security, threat intelligence, compliance — across industries like healthcare, finance, government, and tech.
Average cybersecurity salaries vary by specialization:
- Cyber Security Analyst: $84,000
- Information Security Analyst: $99,000
- Cyber Security Engineer: $111,000
- Penetration Tester: $101,000
- Cyber Security Consultant: $91,000
- Security Architect: $135,000
What are the key responsibilities of a cybersecurity specialist?
What are the key responsibilities of a cybersecurity specialist?
Your work in cybersecurity directly contributes to protecting sensitive information and maintaining the integrity of digital systems. The field of cybersecurity consists of various specialized jobs focused on this goal but approaching it from different avenues. For example, a security analyst monitors and tests networks for security breaches, investigates incidents and makes security enhancement recommendations. Meanwhile, a security consultant advises organizations on best security practices, performs risk assessments, develops security policies, and helps implement tailored security solutions.
During your TripleTen Cybersecurity Bootcamp, you’ll explore these and many other career paths to discover which one is right for you
How do online cyber security classes work?
How do online cyber security classes work?
All you need to start learning is an internet connection and a computer: TripleTen’s learning platform has everything you need, including lessons, practice tasks, and projects. For the part-time track, you study on a flexible schedule, allowing for work and life obligations. At the end of each 2-week sprint (set of lessons), you will complete a project with a deadline. These projects replace traditional tests or quizzes: they are reviewed by cybersecurity professionals, and can be included in your portfolio of work. For the full-time track, you’ll be expected to log in for live, virtual lessons with instructors daily, and projects will be due weekly.
We'll provide a complete overview of the latest industry security practices and requirements. You can consult one-on-one with our instructors, who are happy to share practical knowledge and industry know-how. You’ll also work on projects to boost your understanding of cybersecurity.
Does cybersecurity require coding?
Does cybersecurity require coding?
Programming isn’t mandatory for entry-level cybersecurity jobs, but it helps. Basic IT security just requires networking fundamentals and the CompTIA Security+ certification.
You’ll need programming skills to earn a cybersecurity engineer’s salary, or to break into specific fields, such as application security. Programming knowledge can be leveraged to identify software and web application threats more quickly.
What is the difference between a cybersecurity specialist and an analyst?
What is the difference between a cybersecurity specialist and an analyst?
The difference lies in the scope of their responsibilities. A security analyst monitors an organization's IT systems to identify any potential threat. A security specialist focuses on implementing security measures devised by analysts and consultants, e.g., a specific encryption or networking protocol recommended by analysts.
A specialist works mainly on the ground level, while an analyst works from a bird’s eye view. They both protect organizations from potentially devastating cyber attacks.
What kind of support will I receive?
What kind of support will I receive?
Reviewer feedback on every sprint project, guided tutorials and resources at each stage, and access to study groups and online communities throughout the program. Career coaching support is also part of the experience. The structure is built so you're not figuring things out alone — there are multiple layers of support designed to keep you moving.
Do you offer a money-back guarantee?
Do you offer a money-back guarantee?
Yes, TripleTen offers a full tuition refund if you don't land a new tech job within 10 months of graduation. Here's how you can qualify for the money-back guarantee:
- You must complete the program, including all career counseling and the Active Job Search period
- You need to actively participate in the job search by applying to relevant roles and tracking your applications
- You must be a U.S. resident
Full details and eligibility requirements are outlined in our Terms of Use.
Can I enroll if I have no background in tech or math?
Can I enroll if I have no background in tech or math?
Yes. Our programs are designed to be beginner-friendly, and 80% of our students come from non-STEM backgrounds — so you don't need any coding experience or a tech background to get started. In fact, 61% of TripleTen graduates don't have a bachelor's degree. No matter your educational background, you can still successfully transition into tech.
What makes TripleTen one of the best cybersecurity bootcamps?
What makes TripleTen one of the best cybersecurity bootcamps?
TripleTen is one of the best cybersecurity bootcamps because we are at the forefront of AI-ready career preparation. In 2025, we ensured the Cybersecurity program teaches high-demand AI skills, moving from a traditional "coding bootcamp" model to AI-ready career transition program.
Our cybersecurity bootcamp stands out by offering a truly comprehensive, career-ready education that goes far beyond technical instruction. Students gain hands-on training in critical hard skills — including malware and virus defense, network security, cryptography, and vulnerability testing — while also mastering the soft skills that set top professionals apart, such as risk management, critical thinking, and the ability to communicate complex threats to non-technical stakeholders like executives and legal teams. We also offer on-the-job training through our externship program, as well as personalized career support (resume building, LinkedIn optimization, networking, and interview preparation).
Can TripleTen's bootcamp give me a job placement?
Can TripleTen's bootcamp give me a job placement?
TripleTen does not guarantee job placement, but offers a money-back guarantee if you don't land a job within 10 months of graduating. In 2025, 63% of our grads landed a job within 10 months of completing their program.
TripleTen offers career support services including a dedicated career coach, resume and interview prep, and a job search strategy to give you all the skills to land a role in tech after completing your program.
Is it hard to get a cybersecurity job with just a bootcamp?
Is it hard to get a cybersecurity job with just a bootcamp?
It's competitive, but doable — especially if you graduate with a solid portfolio and a CompTIA Security+ certificate. Junior roles like SOC Analyst or Junior Security Engineer aren't looking for a degree; they're looking for someone who can demonstrate they know the tools and can think through a problem. That's exactly what the coursework and projects in this program are designed to demonstrate.
Does this course prepare you for a cybersecurity certification?
Does this course prepare you for a cybersecurity certification?
Yes. You’ll be preparing for the CompTIA Security+ exam throughout the course. You'll cover all core exam domains — Threats and Vulnerabilities, Technologies and Tools, Architecture and Design, Identity and Access Management, Risk Management, and Cryptography and PKI — through practice exams, concept reviews, and study communities. Passing the exam will count as your capstone project for the course.
What if I don't have enough time to complete the course within the time frame provided?
What if I don't have enough time to complete the course within the time frame provided?
The sprint structure gives you flexibility, and support is available throughout. If you’re falling behind, get ahead of it early — talk to your advisor or coaching team before it becomes a problem. For specific policies on extensions or deferrals, contact TripleTen directly.












